Verizon · Ceres · 2025
AI Deployment Platform for Private 5G Infrastructure
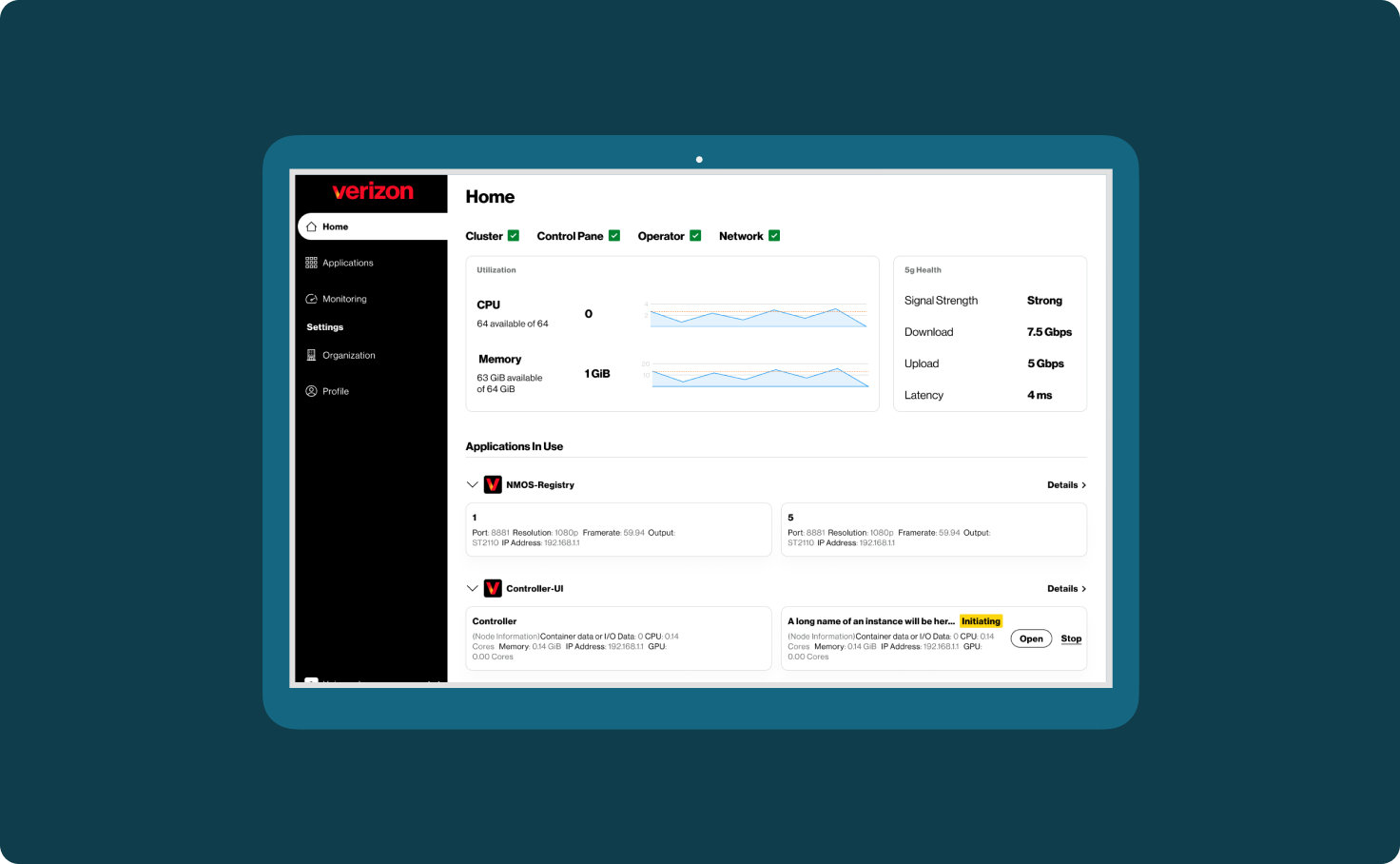
Ceres is Verizon's platform for deploying and managing containerised AI apps over Private 5G. It runs on a 5-node K8s cluster with NVIDIA L40S and H100 GPUs, at 4ms latency in air-gapped venue environments — no cloud dependency.
Senior UX Designer
RBAC UX · Multi-Tenancy · Monitoring
Featured at GTC & NAB 2025
Technical PM · Staff Engineers · DevOps · Client Stakeholders · Hardware Team
The Challenge
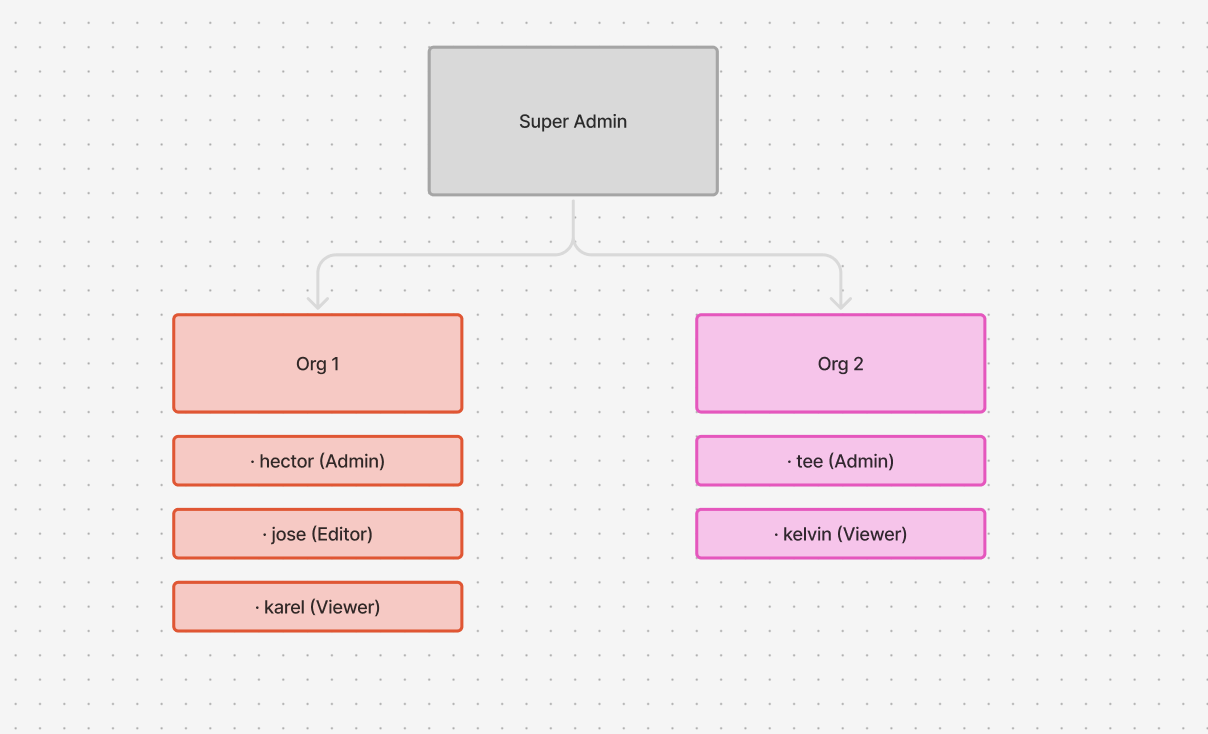
Due to timing, the alpha was designed with a flat structure — allowing everyone from top to bottom full access to everything. Every user had full access to the platform.
The risk is that a single misconfiguration in a K8s 5-node cluster can take down an entire live broadcast, which is disastrous in the M&E space. In live broadcast for example, a focus lapse during a 90-minute match isn't recoverable.
Multiple crews, one cluster, zero interference. I owned the RBAC UX design end-to-end — including Multi-Tenancy and Monitoring UX flows.
Users
Broadcast operators and creators. The key constraint: broadcast crews needed zero K8s knowledge to operate the platform. Every permission decision had to be abstracted away from the underlying infrastructure.
Cluster Admin
Full platform access. Verizon-side technical support.
Org Admin
Full org access. Can assign roles and permissions.
Editors / Viewers
Scoped access only. Zero infrastructure visibility.
Architecture Decisions
Cluster-local auth— air-gapped venues rule out cloud identity providers, so auth runs entirely on-cluster.
Org isolation— one crew stopping a container can't affect another's apps, scoped at the namespace level and enforced through the UI.
Org-scoped context switching— switching orgs re-renders apps, monitoring, and settings to that org's data only.
What I Designed
User Groups & Permissions
Designed role-based access down to the app level, enabling admins to grant video teams specific access without exposing infrastructure controls. Admins can create roles, define permissions, and manage users within each group.
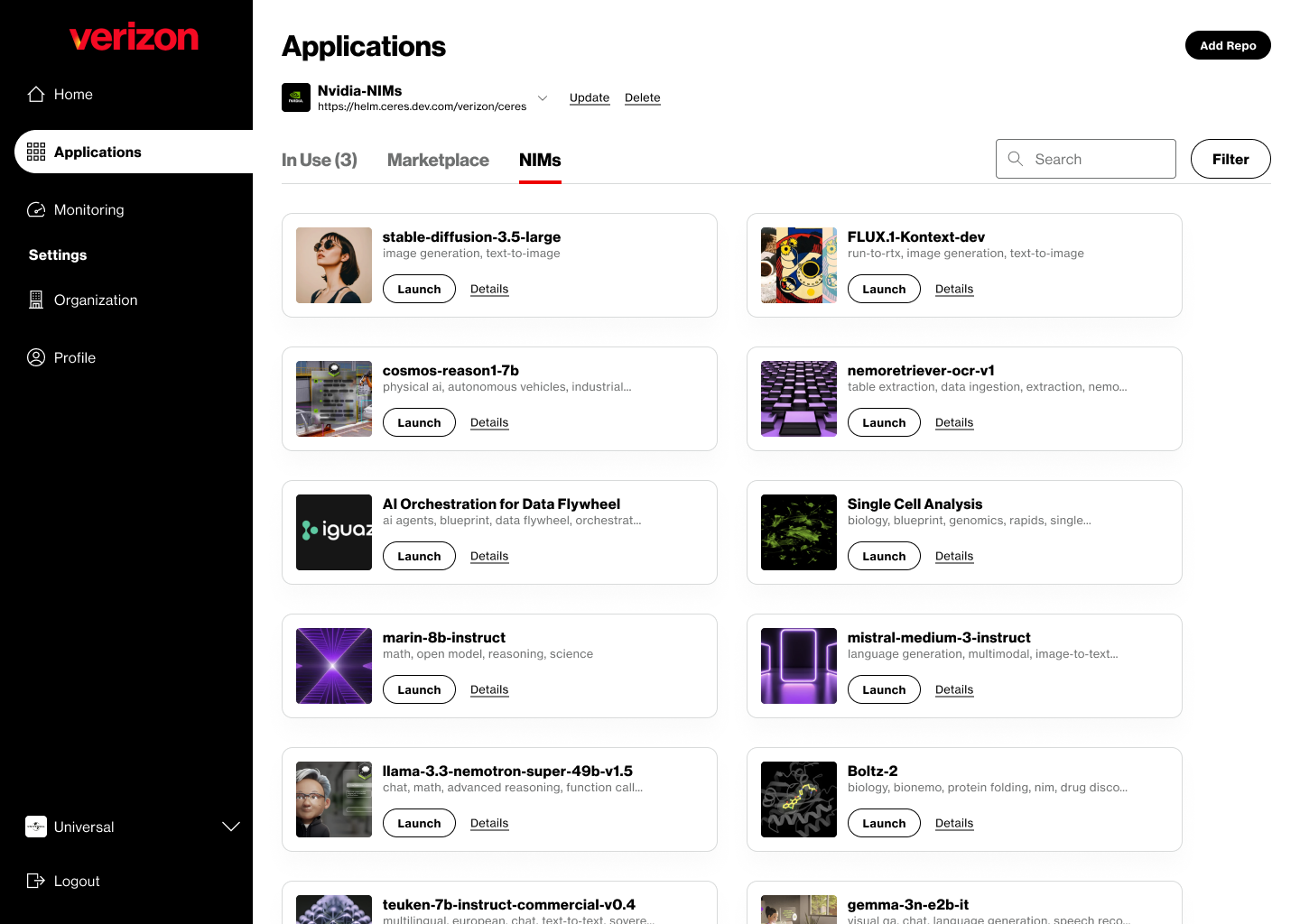
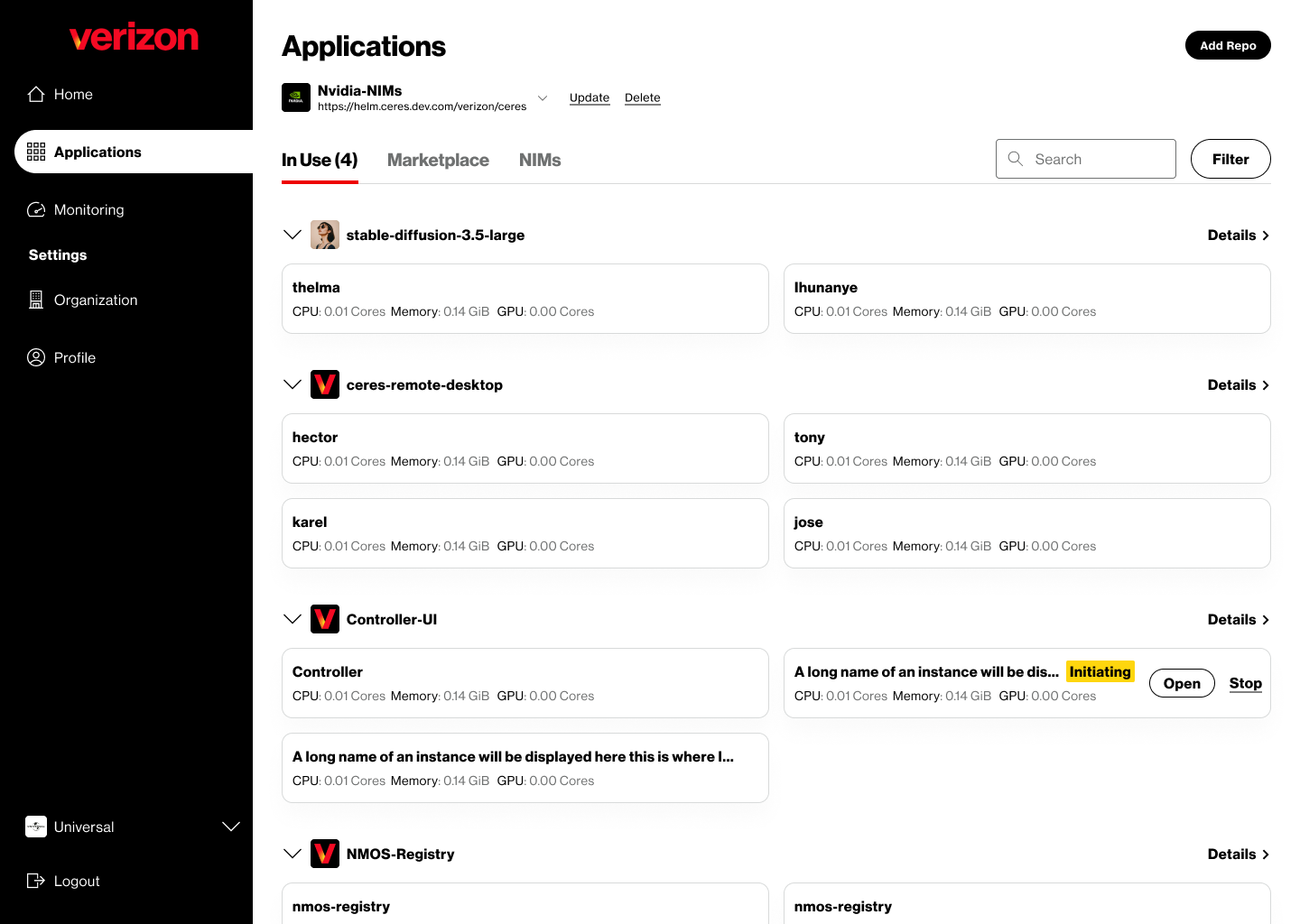
Repo-based Marketplace & Access Control
Designed a repo-scoped model where RBAC is namespaced per repository, powering a marketplace for discovering, installing, and launching apps (including NVIDIA NIMs). Built a repo selector that carries role context, dynamically adjusting visible apps, actions, and installation states per environment.
Instance Management
Designed minimal instance cards that show resource specs by default, with actions revealed contextually based on role. Implemented hover-based admin controls only — balancing progressive disclosure with performance constraints in a multi-node cluster.
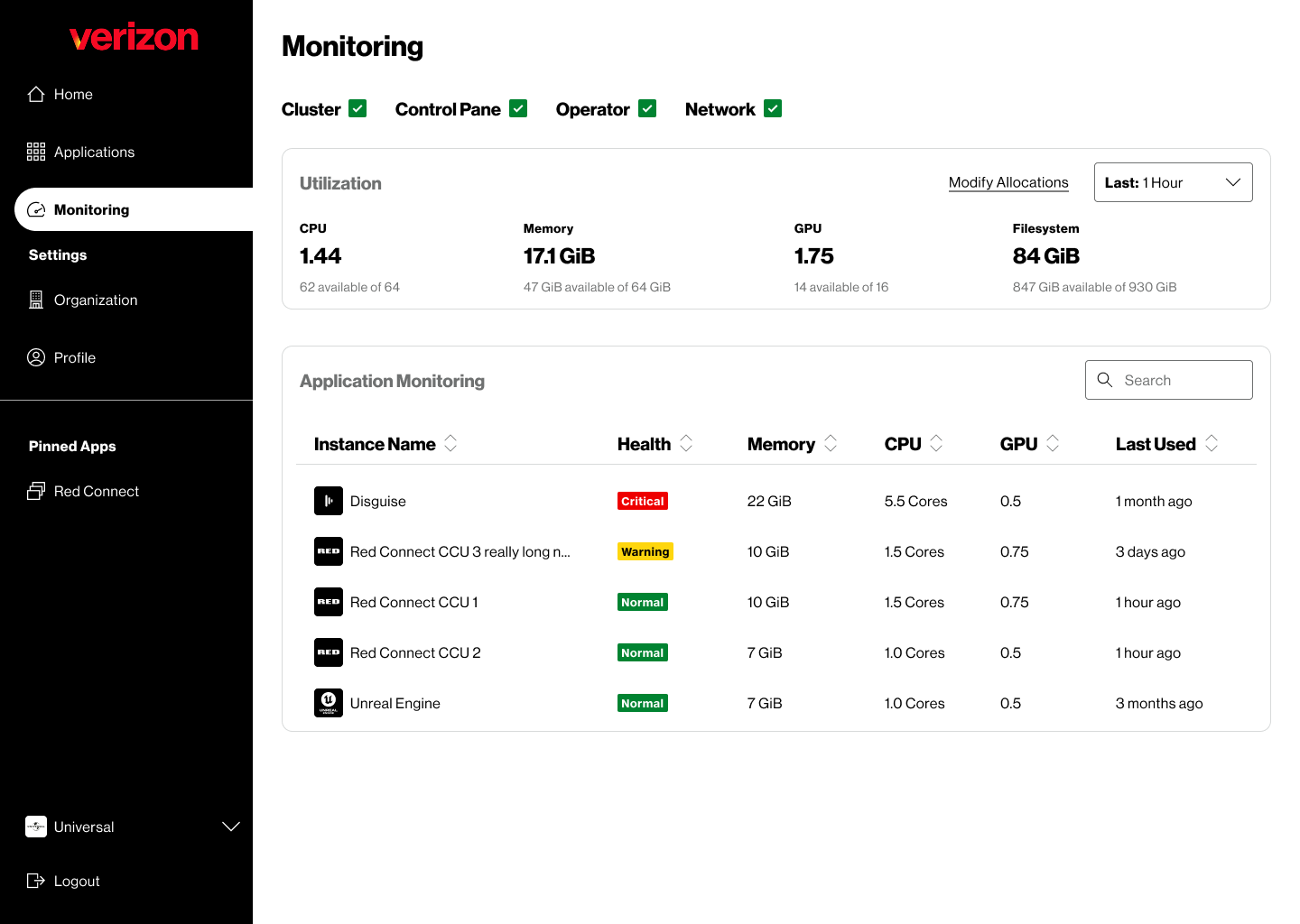
Monitoring & Health Visibility
Designed org and platform-level monitoring to surface resource allocation and flag critical states early — especially during live events where seconds matter.
The Result


Featured at GTC 2025 in a Verizon/Monks speaker session. Live demoed at NAB 2025 with Haivision and FanDuel.